The decentralized revolution of Web3 promises a more open, secure, and user-centric internet. However, this paradigm shift introduces novel security challenges. As the ecosystem matures, so too do the sophisticated methods employed by malicious actors. Understanding the nuances of Web3 security and the growing threat of Web3 data breaches is paramount for developers, businesses, and users alike. This post delves into the current landscape, analyzes recent incidents, and outlines robust strategies for safeguarding decentralized applications and assets.
Understanding the Web3 Security Landscape
Web3, built on blockchain technology, aims to decentralize control and ownership, moving away from the centralized servers of Web2. This fundamental difference creates a unique security landscape. Unlike Web2, where data is often stored in centralized databases managed by a single entity, Web3 data is distributed across a network, making it theoretically more resilient but also introducing new attack surfaces.
- Defining Web3 and its unique security challenges: Web3 refers to the next generation of the internet, characterized by decentralization, blockchain technology, and token-based economics. Its security challenges stem from the immutability of blockchains, the complexity of smart contracts, and the management of private keys.
- Key differences between Web2 and Web3 security models: Web2 security often relies on centralized firewalls, access controls, and data encryption managed by service providers. Web3 security, conversely, emphasizes cryptographic security, user-controlled wallets, and the inherent security of distributed ledgers, but also introduces risks related to smart contract bugs and user key management.
- Common vulnerabilities in Web3 applications (smart contracts, wallets, etc.): Vulnerabilities range from flaws in smart contract code (like reentrancy or integer overflows) to insecure wallet practices (private key compromise, phishing) and exploits targeting decentralized exchanges (DEXs) and NFT marketplaces.
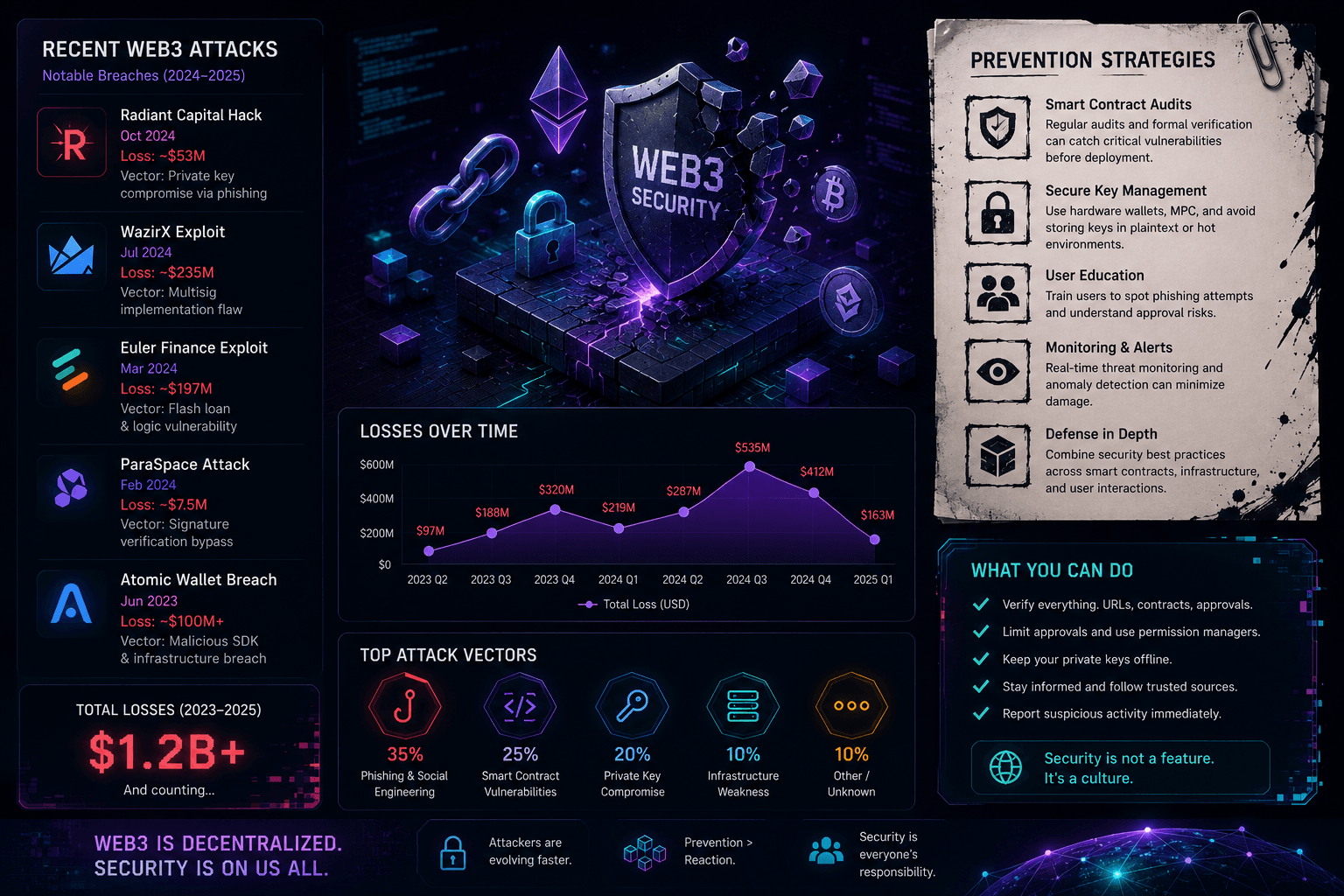
- The increasing frequency and impact of Web3 data breaches: As Web3 adoption grows, so does the attention from cybercriminals. Recent years have seen a significant rise in the value and frequency of hacks targeting DeFi protocols, NFT projects, and other decentralized applications, leading to substantial financial losses and erosion of user trust.
Quick Answer: Web3 Data Breaches and Prevention
Web3 data breaches occur when vulnerabilities in decentralized applications, smart contracts, or user wallets are exploited, leading to the theft of digital assets or sensitive information. Prevention involves rigorous smart contract auditing, secure wallet management practices, implementing robust access controls, and continuous security testing to identify and mitigate risks before they can be exploited.
Case Study: Analyzing Recent Web3 Data Breaches
The history of Web3 is unfortunately punctuated by significant security incidents. One notable example is the Poly Network hack in August 2021, where an attacker exploited a vulnerability to steal over $600 million worth of cryptocurrency. While a large portion was eventually returned, the incident highlighted critical security gaps.
- Detailed analysis of a prominent Web3 data breach (e.g., DeFi hack, NFT marketplace exploit): The Poly Network incident involved a cross-chain bridge exploit. Attackers exploited a vulnerability in how the network handled cross-chain asset transfers, allowing them to mint tokens and drain liquidity from multiple blockchains.
- Attack vector: How the breach occurred (e.g., smart contract vulnerability, phishing attack): The primary attack vector was a vulnerability in the cross-chain communication protocol. The attacker was able to manipulate the system to transfer assets between different blockchains without proper authorization, effectively stealing them.
- Impact assessment: Financial losses, reputational damage, user data compromise: The immediate impact was a staggering financial loss of over $600 million. While the attacker later returned most of the funds, the incident severely damaged Poly Network's reputation and raised serious questions about the security of cross-chain interoperability solutions.
- Lessons learned: Security gaps revealed by the breach: This breach underscored the critical need for comprehensive smart contract audits, especially for complex interoperability protocols. It also highlighted the importance of robust incident response plans and the potential for attackers to exploit even seemingly secure systems.
Common Web3 Attack Vectors and Vulnerabilities
The decentralized nature of Web3, while offering benefits, also presents unique attack vectors that developers and users must understand and defend against.
- Smart contract vulnerabilities (e.g., reentrancy attacks, integer overflows): Flaws in the code of smart contracts are a primary target. Reentrancy attacks allow an attacker to repeatedly call a function before the initial execution completes, draining funds. Integer overflows occur when a mathematical operation results in a value exceeding the maximum representable number, potentially leading to unexpected behavior and exploits.
- Wallet security risks (e.g., private key compromise, phishing attacks): User wallets are the gateways to Web3 assets. If a user's private key is compromised through malware, phishing scams, or insecure storage, their entire digital portfolio is at risk. Phishing attacks often trick users into revealing their private keys or signing malicious transactions.
- Decentralized Exchange (DEX) exploits (e.g., flash loan attacks, front-running): DEXs are susceptible to various attacks. Flash loan attacks leverage uncollateralized loans to manipulate token prices or exploit vulnerabilities in other DeFi protocols. Front-running involves observing pending transactions and submitting a similar transaction with a higher gas fee to execute it first, profiting from price changes.
- NFT-related security threats (e.g., rug pulls, fake NFTs): The booming NFT market has attracted scammers. Rug pulls involve project creators abandoning a project after attracting investment, absconding with funds. Fake NFTs, often sold on compromised marketplaces or through deceptive listings, trick buyers into purchasing worthless or unauthorized digital assets.
Proactive Security Measures for Web3 Applications
Building secure Web3 applications requires a proactive, multi-layered approach to security, integrating best practices throughout the development lifecycle.
- Smart contract auditing and formal verification: Independent security audits by reputable firms are crucial to identify vulnerabilities before deployment. Formal verification uses mathematical methods to prove the correctness of smart contract code, ensuring it behaves as intended.
- Implementing robust access controls and authentication mechanisms: While Web3 emphasizes decentralization, secure access controls are still vital. This can involve multi-signature wallets for critical operations and secure methods for users to interact with dApps without compromising their private keys.
- Regular security testing and penetration testing: Continuous security testing, including penetration testing, helps uncover vulnerabilities that might emerge after deployment or due to evolving threat landscapes. This should include testing for common smart contract exploits and network vulnerabilities.
- Vulnerability disclosure programs and bug bounties: Encouraging ethical hackers to find and report vulnerabilities through bug bounty programs can be highly effective. A clear vulnerability disclosure policy ensures that reported issues are handled responsibly and promptly.
Best Practices for Secure Wallet Management
User-side security is a critical component of the Web3 ecosystem. Educating users and promoting secure wallet management practices can significantly reduce the risk of individual data breaches and asset loss.
- Hardware wallets vs. software wallets: Security considerations: Hardware wallets, which store private keys offline, offer the highest level of security against online threats. Software wallets, while more convenient, are more susceptible to malware and phishing if the device they are on is compromised.
- Multi-signature wallets for enhanced security: Multi-sig wallets require multiple private keys to authorize a transaction, adding a significant layer of security, especially for organizations or shared accounts.
- Secure key storage and backup strategies: Never store private keys or seed phrases digitally in plain text. Use secure offline methods like paper backups stored in multiple safe locations. Avoid sharing seed phrases or private keys with anyone.
- Educating users about phishing scams and social engineering attacks: Users must be vigilant against phishing attempts that mimic legitimate platforms to steal credentials or private keys. Understanding social engineering tactics is crucial for protecting oneself in the Web3 space.
Incident Response and Recovery Strategies
Despite the best preventive measures, security incidents can still occur. Having a well-defined incident response plan is crucial for minimizing damage and facilitating recovery.
- Developing a comprehensive incident response plan: This plan should outline roles, responsibilities, communication channels, and step-by-step procedures for handling various types of security breaches.
- Steps to take immediately following a data breach: Key immediate actions include isolating affected systems, preserving evidence, notifying relevant stakeholders (users, regulators), and initiating the investigation.
- Data recovery and restoration procedures: Depending on the nature of the breach, procedures for restoring compromised data or assets from secure backups must be in place. For immutable blockchains, recovery might involve smart contract upgrades or community consensus.
- Working with law enforcement and regulatory bodies: Cooperating with authorities is essential for investigation and potential recovery of stolen assets. Understanding and complying with relevant regulations is also critical.
The Role of Security Architecture in Web3
A robust security architecture is the foundation of any secure Web3 application. It involves designing security into the system from the outset, rather than treating it as an afterthought.
- Designing secure Web3 systems from the ground up: Security considerations should influence architectural decisions, including the choice of blockchain, consensus mechanisms, and data handling protocols.
- Integrating security into the development lifecycle (DevSecOps): Applying DevSecOps principles ensures that security is a continuous concern throughout development, testing, and deployment.
- Choosing the right security tools and technologies: Utilizing appropriate security tools, such as static and dynamic analysis tools for smart contracts, intrusion detection systems, and secure key management solutions, is vital.
- Staying up-to-date with the latest Web3 security threats and trends: The threat landscape is constantly evolving. Continuous learning and adaptation to new threats and defense mechanisms are essential for maintaining security.
Future Trends in Web3 Security
The future of Web3 security will be shaped by technological advancements, regulatory pressures, and the collective efforts of the community.
- Emerging security technologies (e.g., zero-knowledge proofs, secure multi-party computation): Technologies like zero-knowledge proofs (ZKPs) and secure multi-party computation (SMPC) offer promising ways to enhance privacy and security without compromising functionality.
- The impact of regulation on Web3 security: As governments worldwide grapple with regulating the Web3 space, new compliance requirements and security standards are likely to emerge, potentially increasing security robustness.
- The growing importance of community-driven security initiatives: Decentralized autonomous organizations (DAOs) and community-led security audits are becoming more prevalent, fostering a collaborative approach to security.
- The evolution of Web3 attack vectors and defense mechanisms: Attackers will continue to innovate, developing new exploits. In response, defense mechanisms will evolve, incorporating AI, advanced cryptography, and more sophisticated threat intelligence.
Frequently Asked Questions (FAQ)
- What is the biggest security risk in Web3?
- Smart contract vulnerabilities and private key compromise are often cited as the most significant risks due to their potential for large-scale asset loss.
- How can I protect my Web3 assets?
- Use hardware wallets, secure your private keys diligently, be wary of phishing attempts, and only interact with reputable dApps.
- Are Web3 applications more secure than Web2 applications?
- Web3 offers different security benefits (decentralization, transparency) but also introduces new risks (smart contract bugs, user key management). Neither is inherently 'more' secure; they have different threat models.
BigOsoft: Securing Your Web3 Future
Navigating the complexities of Web3 security requires expertise and robust solutions. At BigOsoft, we understand the unique challenges of decentralized systems and are dedicated to helping you build and maintain secure Web3 applications. Our comprehensive security solutions and expert consulting services are designed to protect your assets, mitigate risks, and ensure the integrity of your decentralized projects. Partner with BigOsoft to fortify your Web3 presence and build with confidence.